Simon Singh is not a man to shirk a challenge. In 1997 he set out to make a documentary about the solving of the world’s most famous (some would say infamous) mathematical problem, Fermat’s Last Theorem. Having bamboozled the planet’s finest mathematical minds for 350 years, Fermat’s challenge had finally been laid to rest by the retiring English mathematician Andrew Wiles. The solution, which took up more than 1,000 pages of densely packed equations, cut a swath through some of the most fiendishly difficult areas in all of math. How on earth could this be presented to a television audience? The marvel is that despite the impenetrability of the math, Singh produced an immensely human and poignant film — seen in the United States on the PBS series “Nova.” He later turned the subject into the bestselling book “Fermat’s Enigma,” which, he tells me, he wrote as an exercise — just to see if he could.
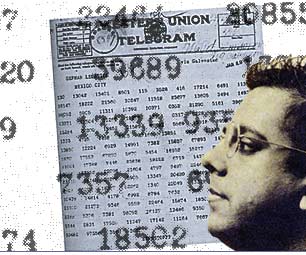
Trained as a particle physicist at Cambridge University — his research topic was the elusive “top quark” — Singh spent several years working at the European Center for Particle Physics (CERN) before swapping a life in the lab for one behind the camera at the BBC’s science department. Who could be better, then, to tackle the subject of cryptography? In his recently published “The Code Book,” Singh follows the development of secret codes from ancient Rome to the latest advances in quantum cryptography. At the end of the book he invites readers to test their own code-breaking skills with a forbidding-looking cipher challenge. The first person to crack all 10 codes will be rewarded with a prize of $15,000 from Singh’s own purse.
It strikes me that there is a continuity between your two books — solving Fermat’s Last Theorem was like cracking a huge mathematical puzzle, and that is not unlike solving a complex code.
If you look at code makers and code breakers, they’re driven by the same things that mathematicians are driven by. They’re obsessive, they love puzzles, they love conundrums. There’s a certain innocence about the code breaker, but at the end of the day, what the code breaker does has a major impact on wars, battles, lives, deaths and so on. Yet all that’s at a much higher level — the political level, the military level. The actual code breaker sitting at his or her desk is a puzzle solver, so there is that in common with mathematicians.
The other thing the two books have in common is that they’re both historical — both go back to 500 B.C., and from my point of view that’s a great context for talking about science.
It’s interesting that history is often seen as an impediment to presenting science. You get the idea from many scientists that all the really good stuff has happened in the last few years, if not last week, and that anything older is out-of-date and irrelevant. But in both books you put the science into a historical context, telling stories with great characters — like Mary, Queen of Scots, and Charles Babbage — and lots of human drama.
From a professional point of view — as a scientist — you always have to strip out the personal perspective. When you write up research papers it’s always in the passive voice: “The beaker was heated,” not “I heated the beaker, and actually that day I was feeling pretty good.” So often it’s difficult for scientists to put in emotional content — though there are some extraordinary exceptions who do. For me, coming from television — where people will switch off if they aren’t engaged — you have to put in the characters and emotional drama. So I write the way I make TV programs.
Is there one story that particularly stands out for you in the history of cryptography?
The story of the British discovery of public-key cryptography [a form of encription technology crucial to the process of putting powerful privacy tools in public hands]. The science of secrecy is a secret science, so often cryptographic work cannot be talked about publicly, sometimes for many years. This story actually only emerged while I was writing the book, this 25-year-old untold story of the greatest discovery in the history of cryptography. It turns out that some years before the Americans came up with public-key encryption, British mathematicians working secretly at the GCHQ [Government Communications Headquarters] had already discovered this, but it was all hushed up because of the military significance. This was the first time these three code makers — James Ellis, Clifford Cocks and Malcolm Williamson — could have their story told, and I feel honored to be able to tell it. The tragedy is that Ellis died just three weeks before the announcement was made, so he never lived to see the credit he deserved.
That doesn’t undermine the work of the American discoveries of public-key encryption. The work they did was quite independent. Furthermore, if they hadn’t made their breakthrough GCHQ might never have gone public, and the information age would never have been where it is now if we didn’t have this breakthrough.
Speaking of secrecy, do you think there are advances in cryptography at the moment way beyond what’s public knowledge?
The whole book is really about the ongoing battle between code makers and code breakers. At the moment most people would say that the code makers are clearly ahead. So it doesn’t really matter if people are coming up with new codes because the ones we have are already very strong. The question is whether there is someone who’s made a big breakthrough in code breaking that we don’t know about — so that the assumption that there’s this big lead isn’t actually true. You can never be sure, but I think it’s unlikely. Although the NSA [National Security Agency] is the world’s largest employer of mathematicians, there are lots of brilliant mathematicians elsewhere who haven’t found any major new algorithms.
So in fact public knowledge at this point in time may be a real reflection of the secret knowledge, so to speak?
Yes, I think that’s the case.
The subtitle of the book is “The Evolution of Secrecy from Mary, Queen of Scots, to Quantum Cryptography,” and early on you make the point that cryptography proceeds in a very Darwinian fashion with a kind of information arms race propelling developments on each side.
It is an evolutionary process, with code makers continually coming up with new developments, and then the code breakers having to respond by evolving new methods for penetrating those defenses. It is like the evolution of predator-prey relationships. It’s interesting too because there are selection pressures. Sometimes it’s only when you’re desperate enough that new breakthroughs happen. For example, when the Germans developed the Enigma code between the wars and ultimately it was the Poles — who were sandwiched between both the Germans and the Russians, and were therefore desperately worried about their national security — who made the first big breakthroughs in cracking these codes. The work was then smuggled out to the British. The Poles are often forgotten in the story, but it really was extraordinary work they did, driven by this pressure of adversity.
We seem to be living at a time when there is a general obsession with codes: not just cryptographic codes, but computer codes and genetic codes — we’ve got the Human Genome Project on the verge of sequencing the entire DNA code of human beings. You also have books like Neal Stephenson’s “Cryptonomicon.”
It’s funny, but when “Fermat’s Enigma” came out there was also “Good Will Hunting” (which was wonderful) and “Pi” (which was terrible), and there were books like “The Man Who Loved Only Numbers” [by Paul Hoffman] and “A Beautiful Mind” [by Sylvia Nasar]. There was a whole series of math films and math books that seemed to enter popular culture at the same time. And now you have a Hollywood film like “Enemy of the State” with Will Smith, and last year’s “Mercury Rising” with Bruce Willis, about the NSA. Also “Cryptonomicon” in literature. I’m sure this won’t be the only book on codes. I’m not sure what triggered this.
Just one of those things that’s in the air. It seems to me that an interest in codes is actually pretty widespread. Children love making up codes and creating secret little languages. Lots of people love the idea of being part of some select group with its own secret passwords, like the Freemasons.
As soon as you express yourself in words, and especially once you start putting words down on paper — whether it’s 10,000 years ago or children today — there’s a realization that you may need to keep these things secret, whether it’s your personal diary or a military strategy. So it’s quite natural that children do this. And it’s empowering. One of the reasons children make codes is to hide things from their parents. To children, parents are almost like Big Brother. We worry about the CIA and the NSA; children worry about their parents. We both use codes to try and protect ourselves.
Lots of people in this country have Big Brother concerns. What do you think about these fears that the government or big corporations are spying on our lives?
If people have that concern then they should just use encryption. The great thing is that encryption is extremely strong, we think there is this big lead, so it should really protect them. The fear is what might happen if governments crack down on encryption and restrict its use. That might happen in Burma or China, but I can’t see it happening in the rest of the world. All the trends are in the other direction.
For the last decade there’s been this big debate between civil libertarians and governments and law enforcement — and it’s been who’s going to win this debate. But what we’re now realizing is that there’s a third force — business, who are on the side of the civil libertarians, because they want strong encryption so they can conduct their business. In France, for example, they recently lifted almost all restrictions on encryption because they didn’t want e-mail companies going off and setting up their businesses elsewhere.
What about the argument that we need governments to be able to crack all encryption codes so they can fight crime, especially organized crime?
If governments ban encryption software it doesn’t really mean much. You can ban a shop from selling software, but you can’t ban somebody downloading it from the Internet or getting access some other way. Even if they did ban all use of such software, there are other ways of proceeding. For instance, I could use a form of steganography and hide a message in a digital image. Whatever the government is doing, people will find ways around it.
Also, the evidence that restricting encryption would help against organized crime is not enormous. If that’s important then you need to find other ways, like “tempest.” [The so-called “tempest attack” is a method whereby you park a van outside someone’s house and monitor the distinct electromagnetic signals given off as they type each computer keystroke.] Or you can send special monitoring viruses into the computers of the people you are watching. There are other technologies you can use that are being developed for these purposes.
My view is that widespread use of encryption would not increase the rate of crime. In fact restricting encryption might do the opposite. If we can’t encrypt our credit card details properly, that might make it easier for criminals. At the moment I don’t see this as a great threat to society — quite the opposite. In 10 years, of course, we might have to reevaluate the whole situation.
Finally, I have to ask about your “Cipher Challenge.” You’re giving away $15,000 of your own hard-earned cash to the first person who cracks all 10 codes at the back of your book. Do you expect anyone to solve it?
I think so and I’ll be happy to give the money away. You can win $15,000 on TV from answering trivial questions, so if anyone can solve this they deserve the prize! The great thing is there’s such a diversity of people working on it. I recently spoke to a Field’s medalist who’s doing it. [The Field’s Medal is the mathematics world’s equivalent of the Nobel Prize.] But when I left England a few days ago, the person who was the furthest along was a 15-year-old girl.
Who are you betting on, the Field’s medalist or the schoolgirl?
[Singh smiles enigmatically, but stays mum.]