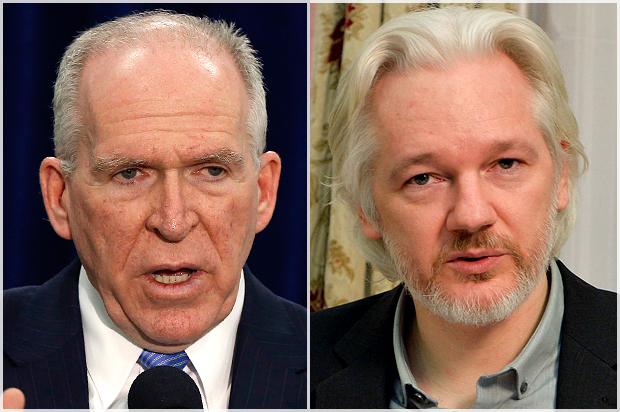
What do China, a 13-year-old stoner, and now, thanks to Wikileaks, the American public all have in common? As of yesterday, they each have a dated copy of CIA Director John Brennan’s application for security clearance from 2008.
The story goes something like this: According to an account from Wired, the teenager in question — who goes by the name “cracka“– did a reverse look up on Brennan, which identified Verizon as his cell phone provider. They called the phone company, pretended to be a Verizon employee, and obtained a bunch of metadata on Brennan’s account, including his backup cell phone number, an AOL email address, and the last four digits of his credit card. They then used that metadata to get AOL to change Brennan’s password on an old email account. By October 12, they were reading his AOL emails, along with the documents he sent to himself as attachments from his old White House email. So these teenagers have these documents — the most sensitive of which is probably Brennan’s security clearance application, if they did in fact obtain that. And according to WikiLeaks, the teenagers shared them with the website, which the website posted yesterday.
The Chinese — who are presumed to be behind the Office of Personnel Management hack identified earlier this year, which reportedly got security clearance forms of U.S. employees and contractors going back to 1985 — would likely have gotten a dated Brennan application in that hack from the period when he wasn’t at CIA.
Brennan has worked for the intelligence community or as a contractor for his entire career, so unsurprisingly his draft clearance application doesn’t show anything really embarrassing. His chief overseas assignment, as Station Chief in Riyadh, Saudi Arabia, in the late 1990s is well known. The leak of the draft security clearance application doesn’t have many details of foreigners he knows, which could be sensitive, but it does include sensitive information on his family, which could expose them to identity theft or other targeting — though it’s likely the intelligence community already acted to respond to such exposure if Brennan was among those targeted in the OPM hack. Nevertheless, this hack has exposed Brennan’s family unnecessarily.
All that said, Brennan makes an unsympathetic victim. Setting aside the legitimate spying he oversees in his role as Director of the Central Intelligence Agency, Brennan authorized his agency to spy on its overseers at the Senate Intelligence Committee last year, based on the unsubstantiated allegation they had “stolen” a document that they in fact had been given. That was a gross violation of separation of powers and as such Brennan has had a part in one of the more breathtaking bits of abusive spying in recent years.
Moreover, the hackers used the very same tools — metadata from Verizon — that the NSA and the rest of the intelligence community have collected on all Americans. (The NSA was not permitted to obtain credit card data under the bulk program that included Verizon, though they did so accidentally on more than one occasion, and the NSA collects passwords via other means.) The intelligence community has long told Americans that they don’t have an “expectation of privacy” in such metadata, and so shouldn’t much care if it gets turned over to spy agencies. But as the hack of Brennan makes clear, that data can be very useful nevertheless, and can easily help spies and hackers access sensitive content.
Finally, this hack exposes the Director of the CIA exercising almost laughable operational security. The files appear to date from the period leading up to Brennan’s appointment as White House Homeland Security Czar, where a big part of Brennan’s job was to prevent hacks in this country. To think he was storing sensitive documents on an AOL server — AOL! — while in that role, really demonstrates how laughable are the practices of those who purport to be fighting hackers as the biggest threat to the country. For at least 6 years, the Homeland Security Czar, then the CIA Director — one of the key intelligence officials throughout the Obama Administration — left that stuff out there for some teenagers to steal.
Hacking is a serious problem in this country. Like Brennan, private individuals and corporations suffer serious damage when they get hacked (and the OPM hack of Brennan’s materials may be far more serious). Rather than really fixing the problem, the intelligence community is pushing to give corporations regulatory immunity in exchange for sharing information that won’t be all that useful.
A far more useful initial step in securing the country from really basic types of hacking would be for people like Brennan to stop acting in stupid ways, to stop leaving both their own and the public’s sensitive data in places where even stoned kids can obtain it, to provide a good object lesson in how to limit the data that might be available for malicious hackers to steal.
Brennan is in the position to offer lessons on operational security to Americans that don’t have his training on how to protect themselves. Instead, he has offered a lesson in how unserious top officials have been in securing America’s data. Let’s hope Brennan’s family remains safe. But let’s also hope that “cracka” convinces our top officials to assess their own actions more seriously.