After a global ransomware attack extending from Russia to the U.S. hit computer systems last week, security analysts quickly realized the perpetrators were using stolen cyber weapons that were part of the National Security Agency’s (NSA) arsenal — for the second time in just six weeks.
While the NSA has yet to acknowledge publicly that their hacking tools have fallen into the wrong hands, at least one congressman asked them to take action. “As a computer science major, my long-term fear — which is shared by security researchers — is that this is the tip of the iceberg and many more malware attacks will soon be released based on NSA’s hacking tools,” Rep. Ted Lieu, D-Calif., wrote in a letter to NSA Director Michael Rogers.
“NSA-created malware has now apparently caused many businesses to grind to a halt, targeted critical infrastructure management systems and ATMs across Europe and Asia, and disrupted the global flow of travel and commerce — including the port of Los Angeles, where some of my constituents are employed,” the letter said. If the agency had any knowledge or information on how to stop the attacks, Lieu said they should “immediately disclose it.” Victims and technology companies have also spoken out, saying “the world isn’t ready for this.”
Yet the government has yet to take any responsibility for weapons that they either developed or purchased. Intelligence officials have said North Korea is responsible for the WannaCry cyberattack in May. NATO announced on Friday that a state actor is once again believed to be behind the most recent attack.
The New York Times elaborated:
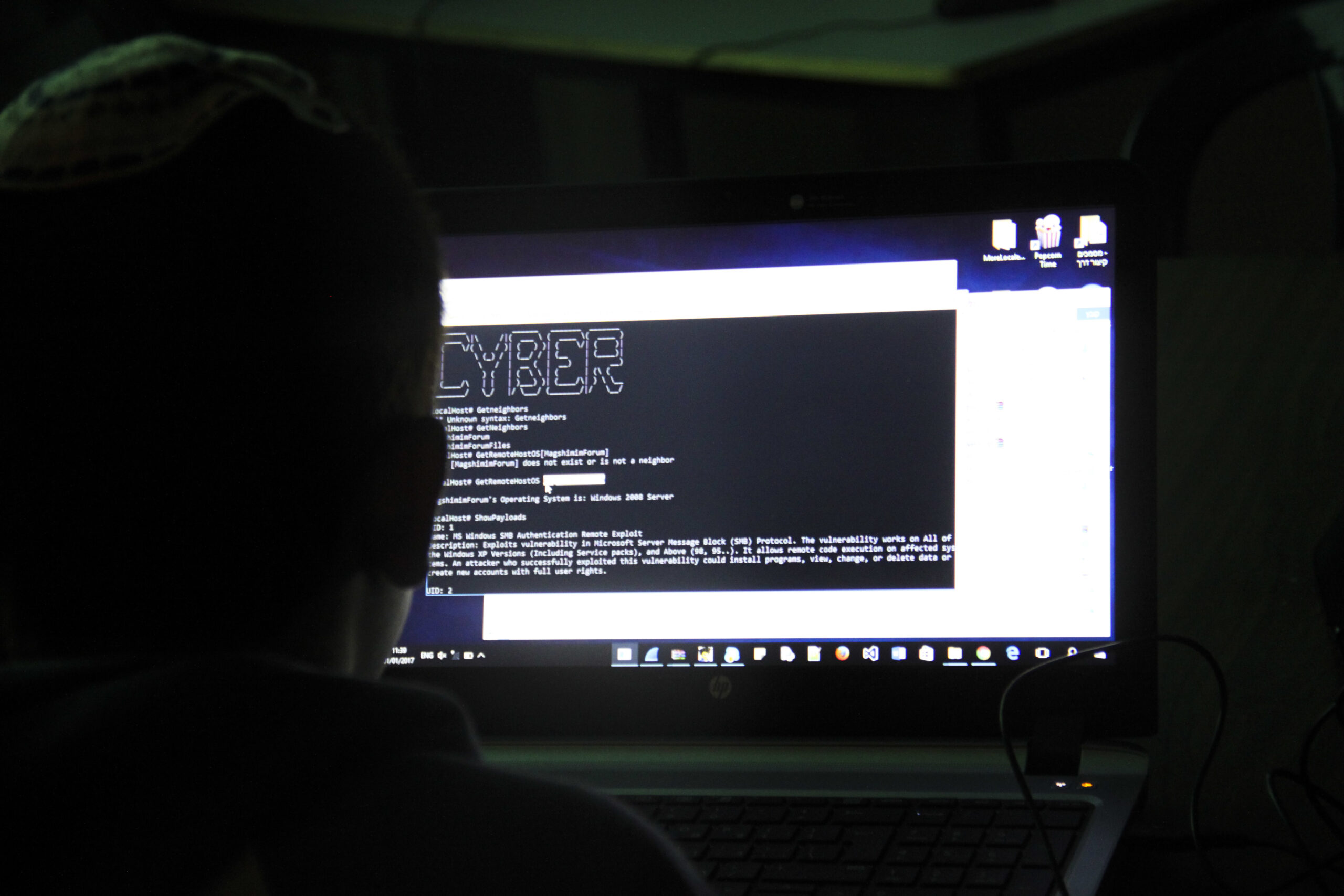
In both cases, the attackers used hacking tools that exploited vulnerabilities in Microsoft software. The tools were stolen from the N.S.A., and a group called the Shadow Brokers made them public in April. The group first started offering N.S.A. weapons for sale in August, and recently even offered to provide N.S.A. exploits to paid monthly subscribers.
“If American espionage cannot protect the special tools that it possesses, it doesn’t matter that they are good people working for good purposes under good oversight,” Michael Hayden, former director of both the NSA and CIA, told NBC News. “If they cannot protect the tools, I just can’t mount the argument to defend that they should have them. This is the one that, unless resolved, I think actually could constitute a legitimate argument to do less.”