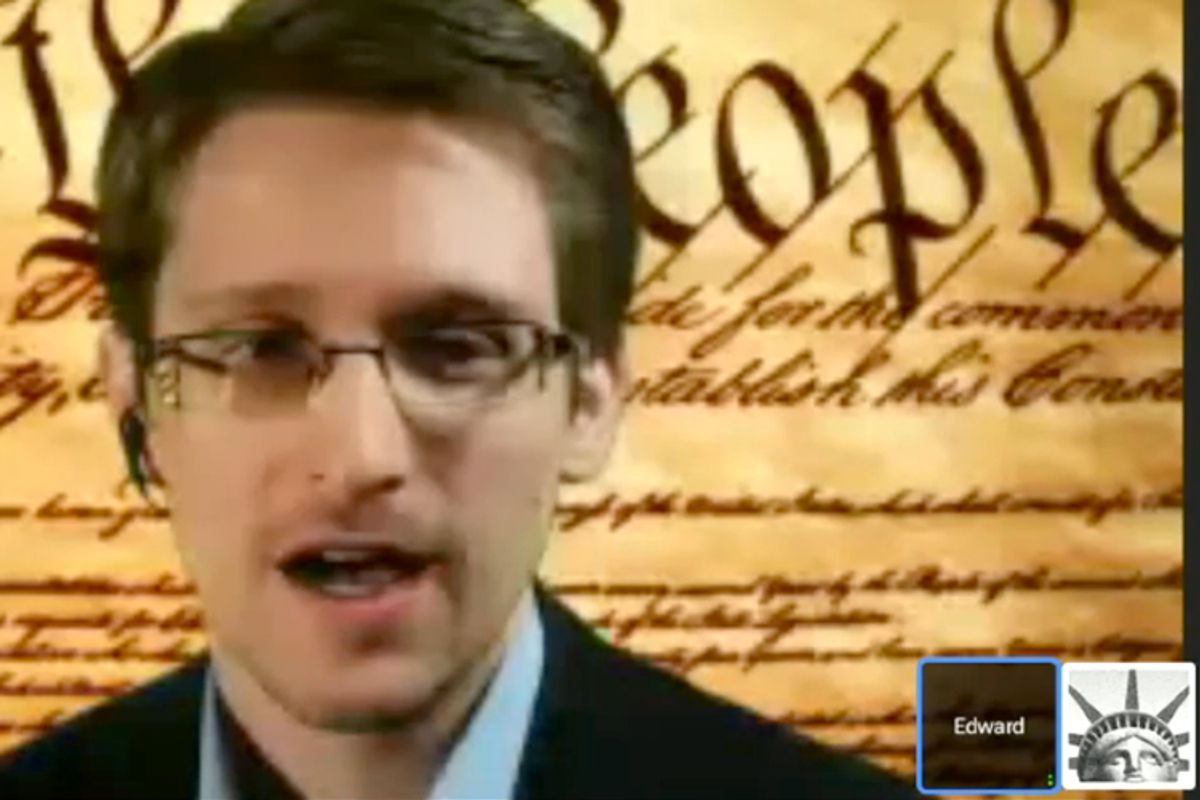
This week Wired published a comprehensive profile of "The Most Wanted Man in the World," Edward Snowden. The seven digital pages of James Bamford's three days with the National Security Agency whistle-blower give a glance at Snowden's back story, and then follow his career trajectory from the Army Special Ops -- where he broke both legs and was discharged -- to the CIA, and then his final stints with NSA contractors Dell and Booz Allen.
Sprinkled into the profile are revelations -- some brand-new, others previously reported -- of our government's abuse of power, mass surveillance and the blasé attitude of fellow workers. Below are the most interesting granules taken from the profile.
Snowden attempted to leave what Bamford called "digital bread crumbs" -- traces to help detect what he'd taken versus what he just "touched." Wired explains below:
"He says that he actually intended the government to have a good idea about what exactly he stole. Before he made off with the documents, he tried to leave a trail of digital bread crumbs so investigators could determine which documents he copied and took and which he just 'touched.' That way, he hoped, the agency would see that his motive was whistle-blowing and not spying for a foreign government. It would also give the government time to prepare for leaks in the future, allowing it to change code words, revise operational plans, and take other steps to mitigate damage. But he believes the NSA's audit missed those clues and simply reported the total number of documents he touched—1.7 million. (Snowden says he actually took far fewer.) 'I figured they would have a hard time,' he says. 'I didn't figure they would be completely incapable.'"
The specter of a possible second, still anonymous, whistle-blower lingers in part of the profile. The profile speculates on the theory, but Snowden himself will not discuss it on the record. Bamford postulates below:
"Snowden himself adamantly refuses to address this possibility on the record. But independent of my visit to Snowden, I was given unrestricted access to his cache of documents in various locations. And going through this archive using a sophisticated digital search tool, I could not find some of the documents that have made their way into public view, leading me to conclude that there must be a second leaker somewhere. I'm not alone in reaching that conclusion. Both Greenwald and security expert Bruce Schneier—who have had extensive access to the cache—have publicly stated that they believe another whistle-blower is releasing secret documents to the media."
The first major new revelation from the profile is that in 2013, the United States, via a group of NSA hackers, was responsible for a country-wide Internet outage in Syria -- amid the civil war. Wired explains:
"By the time he went to work for Booz Allen in the spring of 2013, Snowden was thoroughly disillusioned, yet he had not lost his capacity for shock. One day an intelligence officer told him that TAO—a division of NSA hackers—had attempted in 2012 to remotely install an exploit in one of the core routers at a major Internet service provider in Syria, which was in the midst of a prolonged civil war. This would have given the NSA access to email and other Internet traffic from much of the country. But something went wrong, and the router was bricked instead—rendered totally inoperable. The failure of this router caused Syria to suddenly lose all connection to the Internet—although the public didn't know that the US government was responsible. (This is the first time the claim has been revealed.)"
The second, and probably most important new piece of NSA spying we learn from the profile is the developing of MonsterMind. MonsterMind would not only be an automated response-attack with cyberwarfare, it also requires the analysis of mass amounts of digital traffic -- a blight to privacy.
"The massive surveillance effort was bad enough, but Snowden was even more disturbed to discover a new, Strangelovian cyberwarfare program in the works, codenamed MonsterMind. The program, disclosed here for the first time, would automate the process of hunting for the beginnings of a foreign cyberattack. Software would constantly be on the lookout for traffic patterns indicating known or suspected attacks. When it detected an attack, MonsterMind would automatically block it from entering the country—a 'kill' in cyber terminology.
"Programs like this had existed for decades, but MonsterMind software would add a unique new capability: Instead of simply detecting and killing the malware at the point of entry, MonsterMind would automatically fire back, with no human involvement. That's a problem, Snowden says, because the initial attacks are often routed through computers in innocent third countries. 'These attacks can be spoofed,' he says. 'You could have someone sitting in China, for example, making it appear that one of these attacks is originating in Russia. And then we end up shooting back at a Russian hospital. What happens next?'"
One of Snowden's chief concerns, apart from getting caught by U.S. intelligence, is what he and the profile call "NSA fatigue." Snowden, according to the profile, witnessed his co-workers' jaded indifference to mass surveillance. He hopes that the public does not slowly grow accustomed to mass surveillance.
"Another concern for Snowden is what he calls NSA fatigue—the public becoming numb to disclosures of mass surveillance, just as it becomes inured to news of battle deaths during a war. 'One death is a tragedy, and a million is a statistic,' he says, mordantly quoting Stalin. 'Just as the violation of Angela Merkel's rights is a massive scandal and the violation of 80 million Germans is a nonstory.'"
The entire story is worth a read.
Shares